Hello S-1-1-0!
In previous post I posted about new PowerShell PKI module release and notable enhancements. Today I’ll talk about less notable and obvious, but useful enhancements.
PKCS#10 certificate request support
I made a support for X.509 certificate requests formed in a PKCS#10 format. The only (currently) class is X509CertificateRequest class which is developed in a similar manner as X509Certificate2. Let’s take a spherical horse in a vacuum sample certificate request which was generated by using certreq.exe tool:
[↓] [vPodans] $req = New-Object Security.Cryptography.X509CertificateRequests.X509CertificateRequest "C:\Users\vPodans\D esktop\web.req" [↓] [vPodans] $req Version : 1 RequestType : PKCS10 Subject : CN=web.contoso.com SubjectDN : System.Security.Cryptography.X509Certificates.X500DistinguishedName PublicKey : System.Security.Cryptography.X509Certificates.PublicKey Attributes : {System.Security.Cryptography.Oid, System.Security.Cryptography.Oid, System.Security.Cryptography. Oid} Extensions : {System.Security.Cryptography.Oid, System.Security.Cryptography.Oid, System.Security.Cryptography. Oid, System.Security.Cryptography.Oid...} SignatureIsValid : True SignatureAlgorithm : System.Security.Cryptography.Oid RawData : {48, 130, 4, 120...} [↓] [vPodans]
look, here we see request type, request subject, public key information, optional attributes, extensions, signature algorithm and pure raw copy of the certificate request. Plain and simple. Attributes are implemented as a collection of X509Attribute class (which do not inherit from System.Attribute class) objects and which are similar to X509Extension class. I have implemented a lot of common attribute (within the same class), so you can format them into a readable text by calling Format method:
[↓] [vPodans] $req.Attributes
Oid RawData
--- -------
System.Security.Cryptography.Oid {22, 10, 53, 46...}
System.Security.Cryptography.Oid {48, 56, 2, 1...}
System.Security.Cryptography.Oid {48, 129, 223, 2...}
[↓] [vPodans] $req.Attributes | %{$_.format(1)}
OS Version: 5.2.3790.2
Client Info:
Client ID: 1
Computer name: DC1.contoso.com
User name: CONTOSO\Administrator
Process name: certreq.exe
CSP Info:
KeySpec: 1
Provider: Microsoft Strong Cryptographic Provider
Signature unused bits: 0
[↓] [vPodans]
these attributes are added by certreq.exe automatically. By calling the same method on Extensions property you can get requested extensions in a readable format:
[↓] [vPodans] $req.Extensions
Critical Oid RawData
-------- --- -------
False System.Security.Cryptography.Oid {48, 53, 48, 14...}
False System.Security.Cryptography.Oid {4, 20, 100, 204...}
False System.Security.Cryptography.Oid {48, 10, 6, 8...}
False System.Security.Cryptography.Oid {30, 18, 0, 87...}
False System.Security.Cryptography.Oid {3, 2, 4, 240}
[↓] [vPodans] $req.Extensions | %{$_.format(1)}
[1]SMIME Capability
Object ID=1.2.840.113549.3.2
Parameters=02 02 00 80
[2]SMIME Capability
Object ID=1.2.840.113549.3.4
Parameters=02 02 00 80
[3]SMIME Capability
Object ID=1.3.14.3.2.7
[4]SMIME Capability
Object ID=1.2.840.113549.3.7
64 cc 9a 8d c1 73 f5 ec 6a 5e 39 96 a4 5a 1b fe 50 8a 40 dc
Server Authentication (1.3.6.1.5.5.7.3.1)
WebServer
Digital Signature, Non-Repudiation, Key Encipherment, Data Encipherment (f0)
[↓] [vPodans]
Currently X509CertificateRequest is a base class for requests formed in a PKCS#10 format. There is no support for multi-level and advanced requests (in PKCS#7 and CMC) and I will work on future enhancements. Just need to figure out what enhancements are necessary :)
Certificate Trust List support
Additionally I have added a support (basic) for Certificate Trust Lists (CTLs). CTL is usually used as a container to store some information about certificates. For example, Microsoft Root Certificate Program to implement and organize trust to well-known common public CAs. Since recent time, they are using to store explicitly revoked certificates:
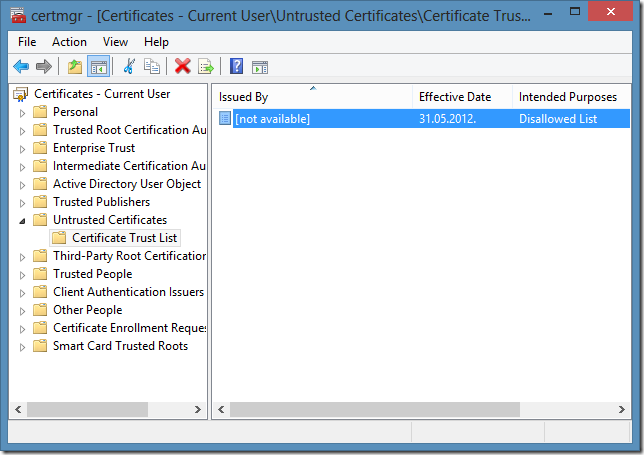
Previously Microsoft stored explicitly revoked certificate and now they are using a CTL to store only necessary information about each revoked certificate and all this information is stored in CTL. Look, how we can work with CTLs in PowerShell with PKI module:
[↓] [vPodans] $ctl = New-Object Security.Cryptography.X509Certificates.X509CTL "C:\Users\vPodans\Desktop\disallowed.stl"
[↓] [vPodans] $ctl
Version : 1
SubjectUsage : {Disallowed List}
SequenceNumber : 01cd3f3facc3ee89
ThisUpdate : 31.05.2012. 18:11:37
SubjectAlgorithm : System.Security.Cryptography.Oid
Entries : {25FB7A5D86F72F5E67288F797305FE94, 6F2D4365C1021F5B8B63EF132BC3B360, AD11DBB76C9CF1AB9998CD842EC1767
3, DFBDD72F99C3B64A797E5AC96D59BE56...}
Extensions : {}
Handle : 561646725904
RawData : {48, 130, 2, 38...}
[↓] [vPodans]
Here we see basic information about CTL itself, intended usage (Disallowed List), when it was generated, certificate entries, optional extensions and pure raw copy of the CTL. Obviously, Entries property contains certificate information:
[↓] [vPodans] $ctl.Entries
Thumbprint Attributes Certificate
---------- ---------- -----------
25FB7A5D86F72F5E67288F797305FE94 {} 0
6F2D4365C1021F5B8B63EF132BC3B360 {} 0
AD11DBB76C9CF1AB9998CD842EC17673 {} 0
DFBDD72F99C3B64A797E5AC96D59BE56 {} 0
C668154BE95E16ADBC321ABC316E384A {} 0
37392E833DC605DD7B38244739939EE3 {} 0
3179FE4B5726D8DB2AAF3DF958C96B97 {} 0
C35A97C80F687DC3C108C6A3339B6846 {} 0
2118A4C6F718CFC7D6D8788C5374D329 {} 0
526A39C04D15862D427FD925AF033690 {} 0
3C36E168ABCC859663ED47A0C05AEE79 {} 0
019E7D56D60DB9ADEC40B967B1BCBA9F {} 0
36CDE99AB8737F86287C583704C95E16 {} 0
26990A77587ED8640184C49366ACB075 {} 0
F69D22AE1ED615B1B9E390E310BBBB31 {} 0
EBE90AD101D3802B8A4C913CACEE6A57 {} 0
1E25F24EDFB0C0042DBB6FBD3C164FB8 {} 0
2CFBA29E2941BD68F66BC8AD30A8CFA0 {} 0
04521AE08FC7F2A38B2CF3F42CA2B2EF {} 0
037B37211FDF7843FAE49F1095C9CC7C {} 0
[↓] [vPodans]
in a given example, only revoked certificates serial numbers are stored without any attributes. If we open a CTL with root certificates, we can extract some attributes for each certificate:
[↓] [vPodans] $ctl = New-Object Security.Cryptography.X509Certificates.X509CTL "C:\Users\vPodans\Desktop\authroot.stl"
[↓] [vPodans] $ctl
Version : 1
SubjectUsage : {Root List Signer}
SequenceNumber : 1401ce72c3b7035d59
ThisUpdate : 27.06.2013. 2:20:15
SubjectAlgorithm : System.Security.Cryptography.Oid
Entries : {CDD4EEAE6000AC7F40C3802C171E30148030C072, 245C97DF7514E7CF2DF8BE72AE957B9E04741E85, 18F7C1FCC309020
3FD5BAA2F861A754976C8DD25, 7F88CD7223F3C813818C994614A89C99FA3B5247...}
Extensions : {}
Handle : 561646725424
RawData : {48, 131, 1, 227...}
[↓] [vPodans] $ctl.Entries[0..4]
Thumbprint Attributes Certificate
---------- ---------- -----------
CDD4EEAE6000AC7F40C3802C171E30148030... {System.Security.Cryptography.Oid, S... 0
245C97DF7514E7CF2DF8BE72AE957B9E0474... {System.Security.Cryptography.Oid, S... 0
18F7C1FCC3090203FD5BAA2F861A754976C8... {System.Security.Cryptography.Oid, S... 0
7F88CD7223F3C813818C994614A89C99FA3B... {System.Security.Cryptography.Oid, S... 0
A43489159A520F0D93D032CCAF37E7FE20A8... {System.Security.Cryptography.Oid, S... 0
[↓] [vPodans] $ctl.Entries[2].Attributes | %{$_.format(1)}
Enhanced Key Usages:
1.3.6.1.5.5.7.3.8 (Time Stamping)
Subject name MD5 hash: 4f f7 db 56 d0 fd 88 a1 9f e3 ba 8b c0 0e 06 62
Subject Key Identifier: 3e df 29 0c c1 f5 cc 73 2c eb 3d 24 e1 7e 52 da bd 27 e2 f0
04 20 5b 78 99 87 f3 c4 05 5b 87 00 94 1b 33 78 3a 5f 16 e0 cf f9 37 ea 32 01 1f e0 47 79 f7 63 53 08
Friendly name: VeriSign Time Stamping CA
[↓] [vPodans]
here we see that all entries have custom attributes and when you call Format method you can get them (though, not for all attributes) in a readable format. In a given example, the certificate in the list is intended for timestamping and it’s friendly name is VeriSign Time Stamping CA. Also, there are attributes that store subject name hash and subject key identifier.
I added Certificate property which should store a handle to a appropriate certificate, however it is always set to zero. Currently I’m in a progress to figure the best way to display such information (create mappings) without filling memory with a ton of unmanaged handles. But in any way, the core (base) functionality is already here and you can use them for your own purposes.
Extended Oid class
Few releases ago I added extended object identifier information retrieval and registration via Get-ObjectIdentifierEx, Register-ObjectIdentifier and Unregister-ObjectIdentifier which provided you with extra functionality and information about particular object identifier. To make it more standard, I developed a Oid2 class which will implement these command functionality (currently only information retrieval is supported).
[↓] [vPodans] New-Object Security.Cryptography.Oid2 "Server Authentication",0
FriendlyName Value DistinguishedName OidGroup
------------ ----- ----------------- --------
Server Authentication 1.3.6.1.5.5.7.3.1 ApplicationPolicy
[↓] [vPodans] [Security.Cryptography.Oid2]::GetAllOids("sha1",0)
FriendlyName Value DistinguishedName OidGroup
------------ ----- ----------------- --------
sha1 1.3.14.3.2.26 HashAlgroithm
sha1NoSign 1.3.14.3.2.26 SignatureAlgorithm
[↓] [vPodans]
here are two examples. In the first example I created a Oid2 object for “Server Authentication” OID. The constructor also added information to which OID group this OID belongs. In the second example, I used static GetAllOids method to retrieve all mappings to a particular OID. One OID may have multiple mappings in different OID groups. As you can see, two OID names are mapped to 1.3.14.3.2.26 OID and they belong to different groups. In the next releases I will complete the rest functionality for OID registration and unregistration.
That’s all about notable enhancements in the current release. I hope this module helps you to simplify MS PKI management in your environments.
Post your comment:




Comments: