Posts on this page:
- Retrieve text messages for Win32 errors
- CA certificates and Untrusted Certificates container
- How to change CA certificate validity period
- How to remove expired user certificates from Active Directory
- You cannot download CA certificate from web enrollment pages
Hi S-1-1-0! Today's topic is described in the post header :)
I guess most of you have encountered with some application/system issues. Sometimes the only information you have is Win32 error code and nothing else. To find a text message for particular error you usually use Google/Bing and/or other tools, like Err.exe from Windows Server 2003 Resource Kit. Yesterday I wrote a PowerShell script that will convert Win32 error code to a readable text. The code uses FormatMessage() WinAPI function. Here is a known limitation, this function doesn't handle network-related errors (that are defined in wininet.h header file). Hopefully my script resolves this limitation by adding a reference to the wininet.dll library when it is necessary. Here is a code snippet:
Read more →
As you may know a DigiNotar CAs was compromised due of some reasons (one, two). Microsoft have decided to break DigiNotar CAs trust at all — http://support.microsoft.com/kb/2607712. Trust breaking is performed as follows:
- DigiNotar CA certificates are removed from Windows Update;
- DigiNotar CA certificates are removed from crypt32.dll on Windows Vista+;
- DigiNotar CA certificates are moved from Trusted Root CAs container to Untrusted Certificates.
Read more →
Today I want to discuss one question about CA certificate validity and how this can be changed.
Issue background
A little abstract. When you install Windows Certification Authority the default value is 5 years. It is quite long period and many young administrators leave default value (especially if they are not very experienced in certificate services). After a time it appears that 5 years is too short validity for CA certificate and administrators lookups for a resolution.
Read more →
Hi S-1-1-0! Today I would like to talk about one of the most requested case — expired user certificate removal from Active Directory.
By default when user requests an authentication and/or encryption certificate from an Enterprise CA it is published to userCertificate property under user account in Active Directory. Published authentication certificate is used for certificate mapping to a user account (or group) and are used by domain controllers during certificate-based authentication. Encryption certificates can be used to provide an access to certain encrypted content. In the case of secure email, sender retrieves recipient's certificate from Active Directory and uses it for mail message encryption purposes. The same process occurs when a user want to provide an access to encrypted file (EFS) for another user. Retrieved certificate is used to re-encrypt symmetric encryption key material.
The negative side here is that certificates sometime expires. If existing certificate is renewed it is added to the userCertificate attribute and expired certificates are not replaced. Certain applications can filter expired certificates and display/select only valid certificates. However other applications may not. In the large environments expired certificates increases Active Directory replication traffic. As the result certain companies performs sanity certificate cleanup on a regular basis. The question here — how can I do this? Lets explore some background and solutions.
Read more →
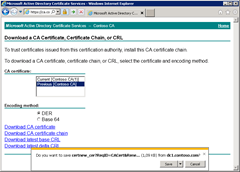
SYMPTOMS
When you try to download CA certificate from web enrollment pages you get a prompt message with unreadable proposed file name:
Do you want to save certnew_cer?ReqID=CACert&Renewal=1&Enc=bin (1,09 KB) from <ServerName>
Read more →