SYMPTOMS
Consider the following scenario. You configured Software Restriction Policies (SRP) to allow run all applications that are signed by the specific signer by creating a Certificate Rule against the signer certificate.
When the policy is refreshed on the client, user cannot run the application, because it is blocked by Software Restriction Policies.
CAUSE
This behavior occurs when the certificate is issued by a Certification Authority (CA) which do not include or provide incorrect issuer information in the Authority Information Access (AIA) extension in the signing certificate. In addition, intermediate CA certificate is not installed in the local store. SRP reads only signing certificate in the digital signature and ignores the rest certificates.
This issue may occur when the signing certificate was issued by Thawte due to their CA certificate distribution policy.
STATUS
This behavior is by design. No bug fixes are available. See Workaround section for example steps to overcome the issue.
WORKAROUND
Perform the following steps to install intermediate CA certificate to local certificate store.
Option 1 is a general guidance for intermediate CA certificate retrieval. Option 2 is used only for signing certificates issued by Thawte.
Option 1
Option 2
The following steps can be used to save Thawte Code Signing CA – G2 certificate to a file:
- Run Notepad;
- Copy the following text and paste it to Notepad:
-----BEGIN CERTIFICATE----- MIIEnDCCA4SgAwIBAgIQR5dNeHOlvKsNL7NwGS/OXjANBgkqhkiG9w0BAQUFADCB qTELMAkGA1UEBhMCVVMxFTATBgNVBAoTDHRoYXd0ZSwgSW5jLjEoMCYGA1UECxMf Q2VydGlmaWNhdGlvbiBTZXJ2aWNlcyBEaXZpc2lvbjE4MDYGA1UECxMvKGMpIDIw MDYgdGhhd3RlLCBJbmMuIC0gRm9yIGF1dGhvcml6ZWQgdXNlIG9ubHkxHzAdBgNV BAMTFnRoYXd0ZSBQcmltYXJ5IFJvb3QgQ0EwHhcNMTAwMjA4MDAwMDAwWhcNMjAw MjA3MjM1OTU5WjBKMQswCQYDVQQGEwJVUzEVMBMGA1UEChMMVGhhd3RlLCBJbmMu MSQwIgYDVQQDExtUaGF3dGUgQ29kZSBTaWduaW5nIENBIC0gRzIwggEiMA0GCSqG SIb3DQEBAQUAA4IBDwAwggEKAoIBAQC3i891W58l2n45sJPbONOpI9CC+ukkflwL joP45npZ5qPFmKeZ0kT/AKalOQSK2imI6tui8xyZFSbCsfT84QxHqQkRBgogkrnH oASMXJQZq1slLB1ifnANzmFs3SuCyc5dSF/3wr68QSMeTyld10+89MUq/GPmfCZO mad5QZ4QSnp5ycaG94aV0ibOPBgq1nzOr82tu/eCLHAmN0XlD0cixgEovS6DXGqk R8Hn0NhrgUY/IRf1B8VDWqZnLLh7YBG1g+71dApycUQ9WP7oGqs4w1nbf244fXbH cmmYNpZX02Yc0lSRBC5UGbDcPbUiXobVKn4g313merFl/sUCTjEtAgMBAAGjggEc MIIBGDASBgNVHRMBAf8ECDAGAQH/AgEAMDQGA1UdHwQtMCswKaAnoCWGI2h0dHA6 Ly9jcmwudGhhd3RlLmNvbS9UaGF3dGVQQ0EuY3JsMA4GA1UdDwEB/wQEAwIBBjAy BggrBgEFBQcBAQQmMCQwIgYIKwYBBQUHMAGGFmh0dHA6Ly9vY3NwLnRoYXd0ZS5j b20wHQYDVR0lBBYwFAYIKwYBBQUHAwIGCCsGAQUFBwMDMCkGA1UdEQQiMCCkHjAc MRowGAYDVQQDExFWZXJpU2lnbk1QS0ktMi0xMDAdBgNVHQ4EFgQU1A1lP3q9NMb+ R+dMDcC98t4Vq3EwHwYDVR0jBBgwFoAUe1tFz6/Oy3r9MZIaarbzRutXSFAwDQYJ KoZIhvcNAQEFBQADggEBAFb+U1zhx568p+1+U21qFEtRjEBegF+qpOgv7zjIBMnK Ps/fOlhOsNS2Y8UpV/oCBZpFTWjbKhvUND2fAMNay5VJpW7hsMX8QU1BSm/Td8jX OI3kGd4Y8x8VZYNtRQxT+QqaLqVdv28ygRiSGWpVAK1jHFIGflXZKWiuSnwYmnmI ayMj2Cc4KimHdsr7x7ZiIx/telZM3ZwyW/U9DEYYlTsqI2iDZEHZAG0PGSQVaHK9 xXFnbqxM25DrUaUaYgfQvmoARzxyL+xPYT5zhc5aCre6wBwTdeMiOSjdbR0JRp1P uuhAgZHGpM6UchsBzypuFWeVia59t7fN+Qo9dbZrPCU= -----END CERTIFICATE-----
- Click File menu and click Save or Save As...;
- In the Save dialog, select the path and file name. Append “.cer” extension to the end of the file name;
- In the Save as type drop-down list, select All Files (*.*);
- Make sure that Encoding drop-down list is set to ANSI:
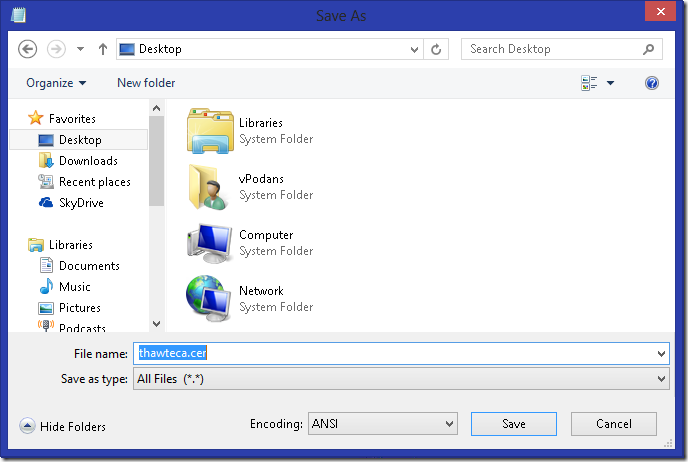
- Click Save button to save the file.
CA certificate installation instructions:
There are three options to install CA certificate to local certificate store:
- Option 1 installs CA certificate to local machine only;
- Option 2 installs CA certificate to a set of computers depending on Group Policy object scope in Active Directory;
- Option 3 installs CA certificate to all machines in the current Active Directory forest
Option 1
- Log on to target computer with local Administrator permissions;
- Run Command Prompt in elevated mode;
- In the Command Prompt, type the following command:
certutil -f –addstore CA path\cacertfile.cer
change “path\cacert.cer” part with actual path and file name. - Close Command Prompt.
Option 2
- Log on to a computer where Group Policy management tools are installed with Domain Admins permissions;
- Run Group Policy Management console (gpmc.msc);
- Edit existing or create a new Group Policy Object (GPO).
- In the GPO editor, expand Computer Configuration\Policies\Windows Settings\Security Settings\Public Key Infrastructure.
- Under Public Key Infrastructure node right-click on Intermediate Certification Authorities and click Import;
- Follow Certificate Import Wizard instructions to import CA certificate;
- Close GPO editor and Group Policy Management console.
When completed, refresh the group policy on the target clients by running “gpupdate /force” command.
Option 3
- Log on to any Active Directory member with Enterprise Administrator permissions;
- Run Command Prompt in elevated mode;
- In the Command Prompt, type the following command:
certutil –dspublish –f path\cacertfile.cer SubCA
change “path\cacert.cer” part with actual path and file name. - Close command Prompt.
When completed, refresh the group policy on the target clients by running “gpupdate /force” command.
Option 3 requires that Autoenrollment policy is enabled on clients.
APPLIES TO
- Windows XP Professional
- Windows Server 2003 (all editions)
- Windows Vista Business, Ultimate, Enterprise
- Windows Server 2008 (all editions)
- Windows 7 Professional, Ultimate, Enterprise
- Windows Server 2008 R2 (all editions)
- Windows 8 Professional, Enterprise
- Windows Server 2012 (all editions)
- Windows 8.1 Professional, Enterprise
- Windows Server 2012 R2 (all editions)
I'm hoping to get Microsoft-signed binaries to work when launched from %localappdata% or %temp% and there's a Disallowed default rule in SRP. There seems to be several publisher certificates for "Microsoft Corporation" and they work individually if added as SRP rules, but they are all in turn signed by one or two "Microsoft Code Signing PCA" intermediate CAs.
If I import these intermediate CAs to Intermediate Certificate Authorities like this page describes, can I then make a certificate rule that uses these intermediate CAs instead of all of those individual publisher certs?
It would have been better if MS didn't try running automatic updates and OneDrive out of %temp% or %localappdata%; this started being a problem in Windows 10. Windows 8.1 didn't have this problem.
> can I then make a certificate rule that uses these intermediate CAs instead of all of those individual publisher certs
no, you can't. SRP relies on direct publishers. It is possible to create more general (less-specific) publisher rule, but not in SRP.
> It would have been better if MS didn't try running automatic updates and OneDrive out of %temp% or %localappdata%; this started being a problem in Windows 10. Windows 8.1 didn't have this problem.
this started being a problem long time ago. Since Windows 7, maybe. OneDrive was the first such application. Now, more and more consumer applications use %appdata% to store and run their binaries, Open Live Writer, Telegram, Google Chrome and many others.
I wish to have Applocker available not only to enterprise customers who purchase Enterprise SKUs, but to small business and even to home users too. And wish to grab all good from SRP and all good from Applocker. At this point, both solutions (SRP and Applocker) have really annoying problems (including management) and neither is ideal. SRP provides more control on policy enforcement, while lacks in rule collection grouping and targeting. Applocker solves these problems, however, their Publisher rules are somewhat too generic and from management point Applocker is inefficient. You cannot temporarily disable Applocker enforcement without overwriting local policies. And, the biggest issue with Applocker: it is simply unavailable to most customers.
Добрый день.
Прошу Вас помочь с непонятным поведением srp.
В домене есть общая групповая политика c srp для всех пк в домене. В ней правила применимые для большинства пк.
Из за однойго правила на хеш библиотеки - не работает vipnet монитор.Выяснил это методом лобового перебора. Самое поганое то что программа не запускается, а в логах самой srp (описал в реестре куда класть логи) тинаша.
Правило на хеш разрешающее и библиотека к vipnet отношения вообще не имеет. Так же ее нет и на самом компьютере.
Вот ссылка на эту dll.
https://cloud.mail.ru/public/K7hi/xXHHMM391
Возможно, вы поймали какой-то побочный эффект в SRP. К сожалению, тут никак помочь нельзя. Если вы точно изолировали проблему, тогда надо решать её как-то иначе. Например, использовать другое правило для DLL (правило сертификата).
Vadims, like Gordon I have a need to allow certain microsoft software to run from %localappdata% but have an SRP whitelist. Teams and Onedrive are the two in particular. Problem I've run into is that it seems Teams and OneDrive have multiple different certs (one for the downloaded .exe which extracts to a temp folder in %localappdata% that then runs another .exe to perform install) and they change pretty frequently.
With AppLocker you should be able to allow anything signed by the publisher (Signed by O=MICROSOFT CORPORATION, L=REDMOND, S=WASHINGTON, C=US) and product name (Teams or OneDrive). That should work to prevent the constant need to update the certs. But of course Applocker is only available to Enterprise and Education which leaves pretty much every SMB customer out in the cold.
I assume your response above about being possible to create more general publisher rules but not with SRP was about AppLocker?
Is there no other way to accomplish this more generic publisher rule outside of AppLocker?
Thanks.
Certificate rules are not enabled by default.
See "Enabling certificate rules" in https://docs.microsoft.com/en-us/windows-server/identity/software-restriction-policies/work-with-software-restriction-policies-rules#BKMK_3
Kind regard,
Remigiusz
Post your comment:




Comments: